Microsoft unmasks Russia-linked ‘GooseEgg’ malware
Researchers at Microsoft say they have uncovered a malicious tool used by Russian state-sponsored hackers to steal credentials in compromised networks.
The malware, named GooseEgg, exploits a vulnerability labeled CVE-2022-38028 in the Windows Print Spooler service, which manages printing processes. The researchers say GooseEgg appears to be exclusive to a group it tracks as Forest Blizzard, which is associated with Russia’s military intelligence agency, the GRU.
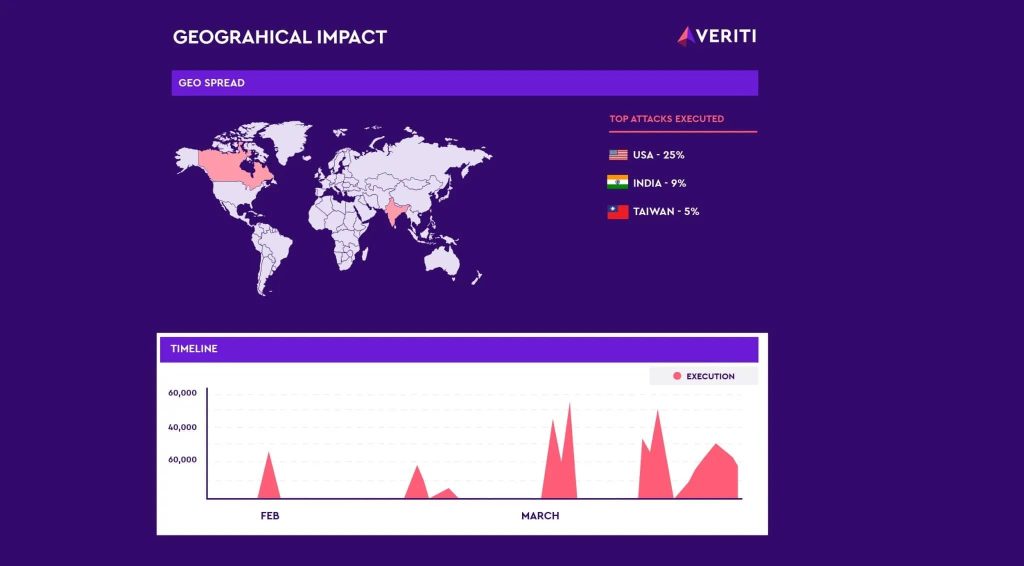
According to the report, Forest Blizzard — as also known as Fancy Bear and APT28 — has been deploying the malware since at least June 2020 against state, nongovernmental, education and transportation organizations in Ukraine, Western Europe and North America.
“The use of GooseEgg in Forest Blizzard operations is a unique discovery that had not been previously reported by security providers,” researchers said.
Microsoft has observed that after obtaining access to a target device, Forest Blizzard uses GooseEgg to elevate privileges within the network. GooseEgg itself is a simple launcher application, but it allows attackers to undertake other actions such as remote code execution, installing a backdoor and laterally moving through compromised networks.
The company patched the Print Spooler security flaw in 2022. “Customers who have not implemented these fixes yet are urged to do so as soon as possible for their organization’s security,” Microsoft said.
In addition to CVE-2022-38028, Forest Blizzard exploits other bugs, such as CVE-2023-23397, which affects all versions of Microsoft Outlook software on Windows devices.
Earlier in December, Microsoft warned that Forest Blizzard has been attempting to use the Microsoft Outlook bug to gain unauthorized access to email accounts within Microsoft Exchange servers since as early as April 2022.
The GRU hackers typically target strategic intelligence assets such as government, energy, transportation and nongovernmental organizations in the U.S., Europe, and the Middle East.
Microsoft has also observed Forest Blizzard targeting media organizations, information technology companies, sports organizations and educational institutions.