HP LaserJet Pwned By Hackers Gets Turned Into An AC/DC Cranking Boombox
These “white hat” hackers hunt for security holes and application exploits, then report them to vendors to claim bug bounties, but some vendors are either unwilling to pay for such services or are simply difficult to contact. Back in 2005, Trend Micro set up the Zero Day Initiative for exactly that reason. It’s a group that works with security researchers to identify “zero-day” vulnerabilities in tech products and then act as an intermediary with the vendors to see them fixed.
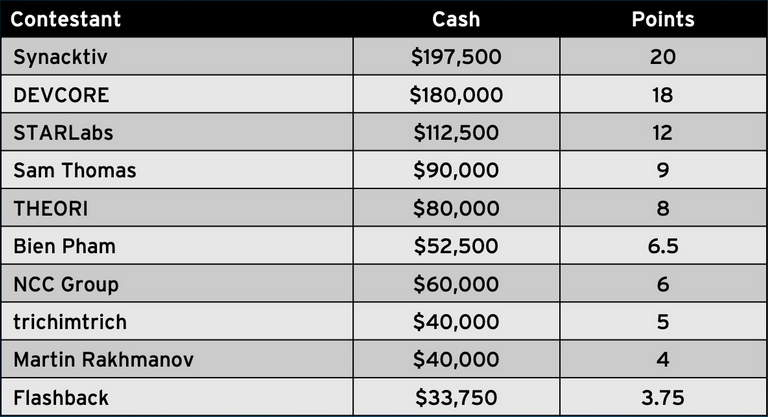
The Zero Day Initiative sponsors multiple yearly events called Pwn2Own, where hackers gather to make time-limited attempts to exploit specific products. This year’s event in Austin was the largest-ever, with 58 total entries from 22 different security teams. Contestants have 30 minutes to deploy their exploit and gain unapproved privileges, remote code execution, or other unauthorized access to their targets.
Not to worry, though; the ZDI doesn’t disclose or publish the exploits…