Hackers Targeting Italian Corporate Banking Clients with New Web-Inject Toolkit DrIBAN
Italian corporate banking clients are the target of an ongoing financial fraud campaign that has been leveraging a new web-inject toolkit called drIBAN since at least 2019.
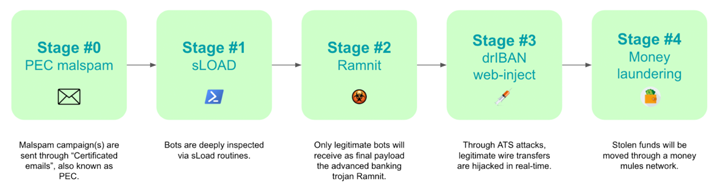
“The main goal of drIBAN fraud operations is to infect Windows workstations inside corporate environments trying to alter legitimate banking transfers performed by the victims by changing the beneficiary and transferring money to an illegitimate bank account,” Cleafy researchers Federico Valentini and Alessandro Strino said.
The bank accounts, per the Italian cybersecurity firm, are either controlled by the threat actors themselves or their affiliates, who are then tasked with laundering the stolen funds.
The use of web injects is a time-tested tactic that makes it possible for malware to inject custom scripts on the client side by means of a man-in-the-browser (MitB) attack and intercept traffic to and from the server.
The fraudulent transactions are often realized by means of a technique called Automated Transfer System (ATS) that’s capable of bypassing anti-fraud systems put in place by banks and initiating unauthorized wire transfers from a victim’s own computer.
Over the years, the operators behind drIBAN have gotten more savvy at avoiding detection and developing effective social engineering strategies, in addition to establishing a foothold for long periods in corporate bank networks.
Cleafy said 2021 was the year when the classic “banking trojan” operation evolved into an advanced persistent threat. Furthermore, there are indications that the activity cluster overlaps with a 2018 campaign mounted by an actor tracked by Proofpoint as TA554 targeting users in Canada, Italy, and the U.K.
The attack chain begins with a certified email (or PEC email) in an attempt to lull victims into a false sense of security. These phishing emails come bearing an executable file that acts as a downloader for a malware called sLoad (aka Starslord loader).
A PowerShell loader, sLoad is a reconnaissance tool that collects and exfiltrates information from the compromised host, with the purpose of assessing the target and dropping a more significant payload like Ramnit if the target is…